Security — Data on the Loose
Security of information seems to be more insecure these days. Witness the hacking of Google accounts in China in attempts to identify dissidents.
SecureWorks, an information security service for 82 healthcare companies reported that the number of hacker attempts doubled in the fourth quarter of 2009. No similar increase was found in the other companies that SecureWorks protects.
Here in the U.S., HIPAA Privacy laws require that notification be made to those affected by a security breach. The HITECH Act’s expanded breach notification requirements will likely result in the discovery and reporting of more such incidents. Business Associates of Covered Entities as defined in HIPAA are considered the least prepared given the new law expands their responsibilities for security and privacy protection.
At the same time, the public is concerned about the privacy of their healthcare information. With the push toward electronic health records and sharing of health information to improve the quality of care, the public must be comfortable that their information is safe from hackers and unauthorized access within an enterprise from the curious, malicious, or security-ignorant caregivers.
BlueCross BlueShield of Tennessee has announced that it has spent more than $7 million to respond to a security breach that might have compromised members’ personal and health data.
What kinds of things can be done to minimize a breach?
Courses of Action
The chart* below shows security actions and examples of each. The vertical axis represents dealing with Causes and Effects; the horizontal axis represents timing – divided into Reactive and Proactive.
Efforts to protect healthcare data should focus on causes with efforts focused on preventive action (upper right quadrant). Preventive actions will result in a barricade that does not allow accidental intrusions, is effective against simple attacks and will keep sophisticated attacks at bay. These are the most effective actions because they prevent a breach from occurring.
Contingency actions are used in case prevention fails. They are backups in case prevention fails. With the fast pace of technology, * Chart adapted from Process Visuals, 2006 by Dr. Alan Weiss. new types of attacks are constantly being created and planning for the unknown is a necessity.
Corrective and adaptive actions can only be performed after an attack or breach has been committed.
Security Action Types
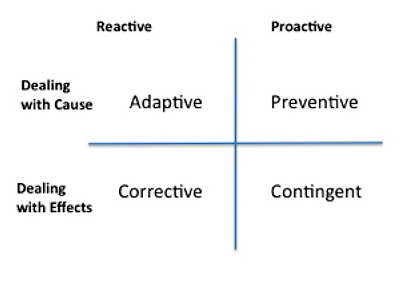
Dealing with an Effect Proactively is a Contingent action. Examples: Logs and audit trails are in place to identify breaches. Dealing with a Cause Proactively is an Adaptive action. Determine how the breach occurred and remediate the cause. Examples: Individual was given more access than required to perform his or her job, individual should have been removed from list of approved users, or badge entry key was not canceled or returned. The action here is to enforce the process of removing invalid users from the system immediately.
Dealing with a Cause Reactively is an Adaptive action. Determine how the breach occurred and remediate the cause. Examples: Individual was given more access than required to perform his or her job, individual should have been removed from list of approved users, or badge entry key was not canceled or returned. The action here is to enforce the process of removing invalid users from the system immediately.
Dealing with an Effect Reactively is a Corrective action. Examples: Locate and close off the breach, investigate and determine if preventive processes are in place, if there are weaknesses in existing processes, apply a temporary solution, and notify affected parties. In the case of lost physical data, determine what data was accessed or taken, by whom and why, and notify affected parties. These are the most time consuming and expensive activities.
Time and money spent on preventive measures are well worth the investment. The cost to report and notify affected parties when a breach occurs is expensive not only in terms money, but also in damage to an organization’s reputation. Every organization should review their security activities each year to determine that existing processes and procedures are working as expected, implement additional protection, remove or replace protections that are no longer appropriate or don’t work, and test the system in its entirety.
That is how to ensure data is safe in your house.
* Chart adapted from Process Visuals, 2006 by Dr. Alan Weiss.

